Part3 - Installing Web Application Proxy for ADFS
Web Application Proxy comes under the Remote Access role and it allows administrators to publish applications for external access.
It is recommended to have WAP servers as standalone (not joined to a domain) and placed in the DMZ. Generally, 2 NICs are used on this server and the first adapter must be connected to the internal network, and the second adapter must be connected to the external network; Internet or public DMZ network.
In this Lab, I dont have DMZ or Internet network. I have 2 servers as WAP and these servers are added into a NLB Cluster.
If you are going to have multiple WAP servers like I do, create a NLB Cluster and add WAP servers into that NLB Cluster. This article explains how to create a NLB Cluster.

Normally we would use an externally bought certificate, but for my lab I generate certificates from Internal CA. WAP servers are not in the domain. That means, I can not request a new certificate from WAP servers but I can make a new request from ADFS server and export that certificate from ADFS and Import it into WAP servers.
On ADFS server:
Just start MMC>File>Add/Remove Snap-In> Certificates > Add > Computer Account >Local Computer > Hit OK.
Then navigate to Personal / Certificates >Right click on Certificates and choose All Task > Request a new certificate.

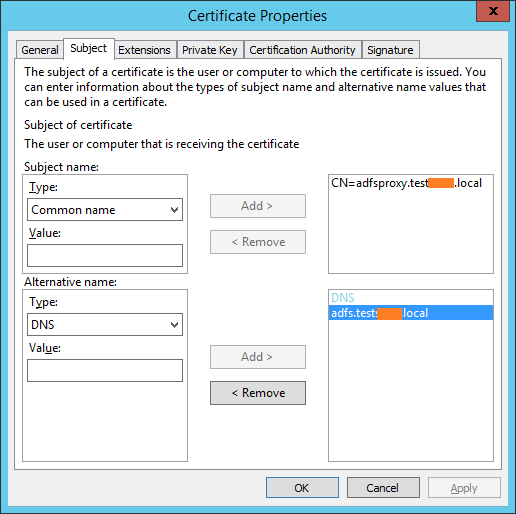
Subject name selected as Common Name and it points the NLB Cluster address for WAP.
We also add Alternative name as DNS and it points the NLB Cluster address of ADFS.
Just start MMC>File>Add/Remove Snap-In> Certificates > Add > Computer Account >Local Computer > Hit OK.
Then navigate to Personal / Certificates >Right click on Certificates and choose All Task > Import > Import the ADFS certificate by completing the wizard.
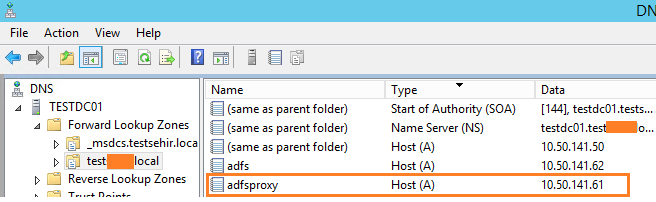
On DNS server I created Host A record for NLB Cluster address
And Then, Edit Web Application Proxy server/s hosts file (located under C:\Windows\System32\drivers\etc ) add the addresses of web application proxy servers.
------------HostsFile------------------
10.50.141.56 TestADFSPrxy1
10.50.141.57 TestADFSPrxy2
-------------------------------------------
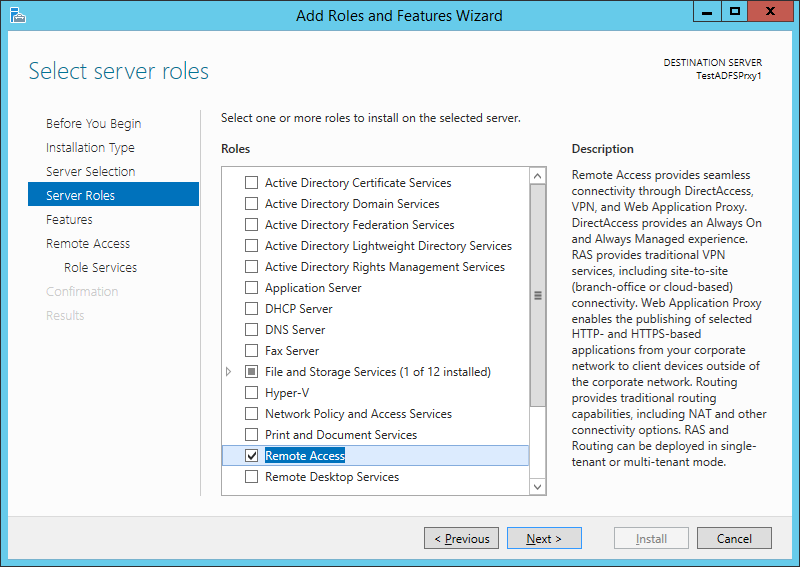
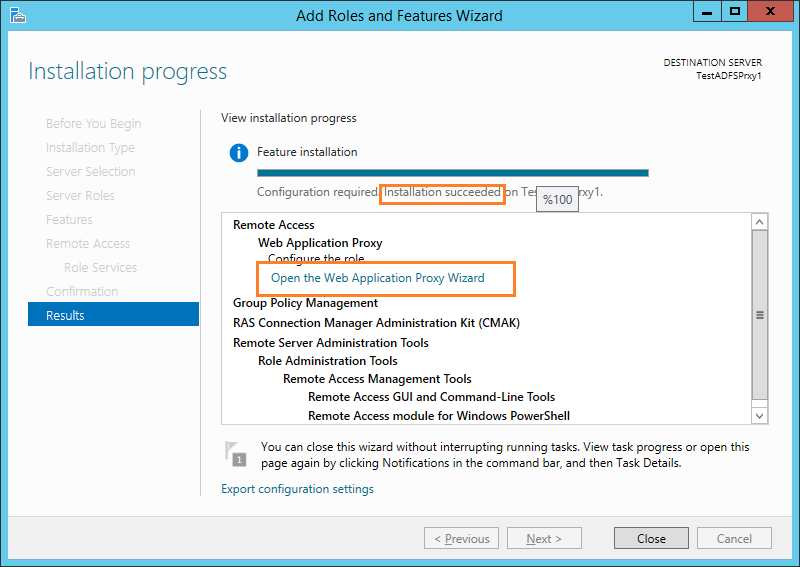
Start Server Manager> Add roles >Choose Remote Access
Just Skip the features section, go with the defaults
Select Web Application Proxy

Click Export Configuration Settings and save it. Now click Install

After Installation Succeded msg appeared, click on the "Open the Web Application Proxy Wizard" link

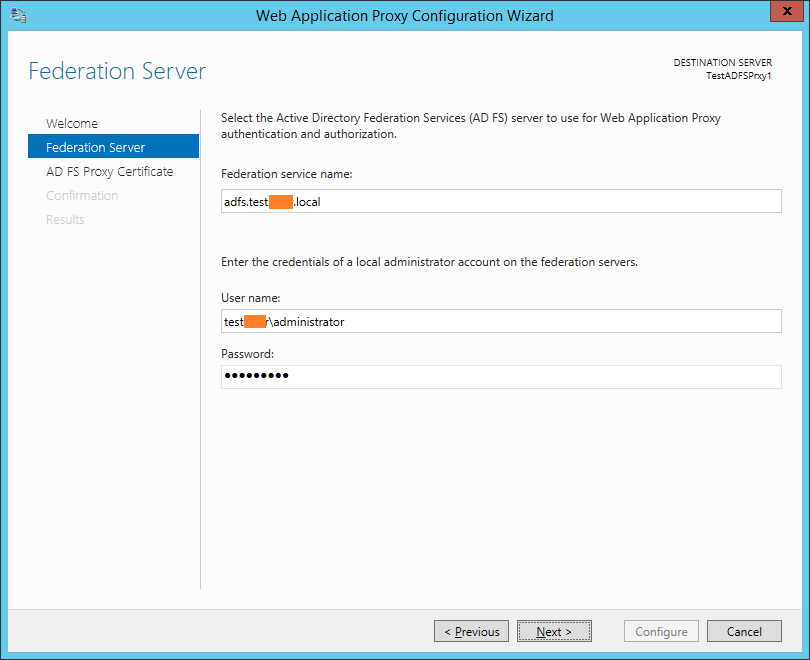
The account asked here will be used only once to create a proxy trust. It will not be stored. I used domain administrator account here.
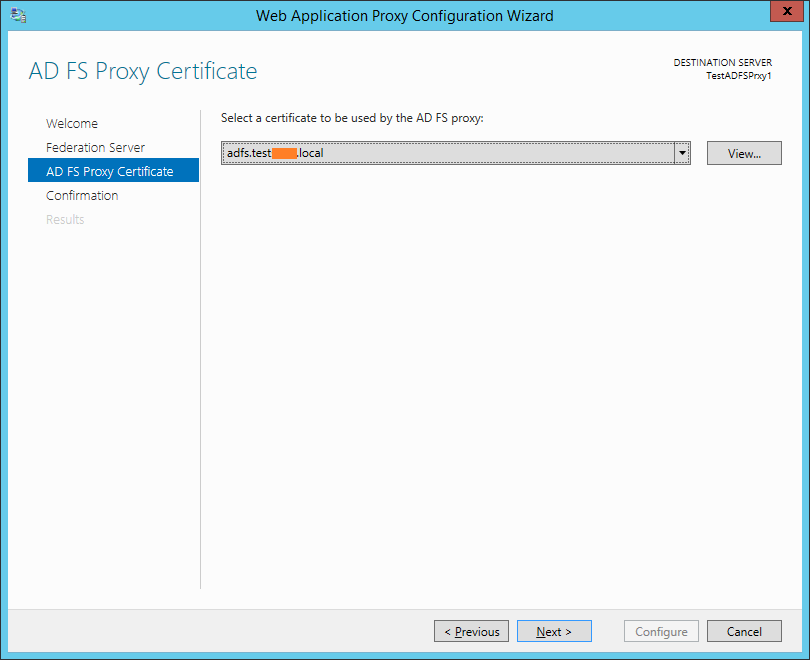
Select the ADFS certificate
Click Configure.
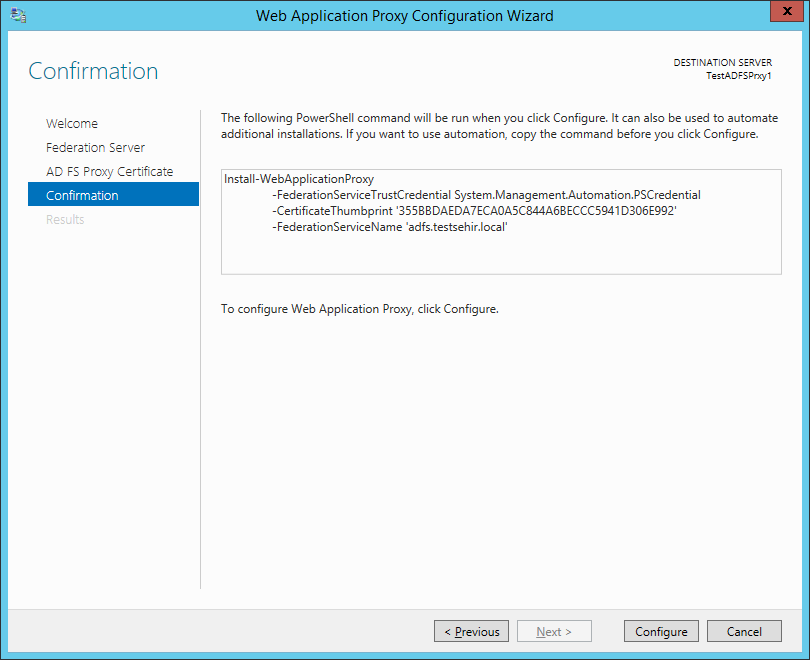
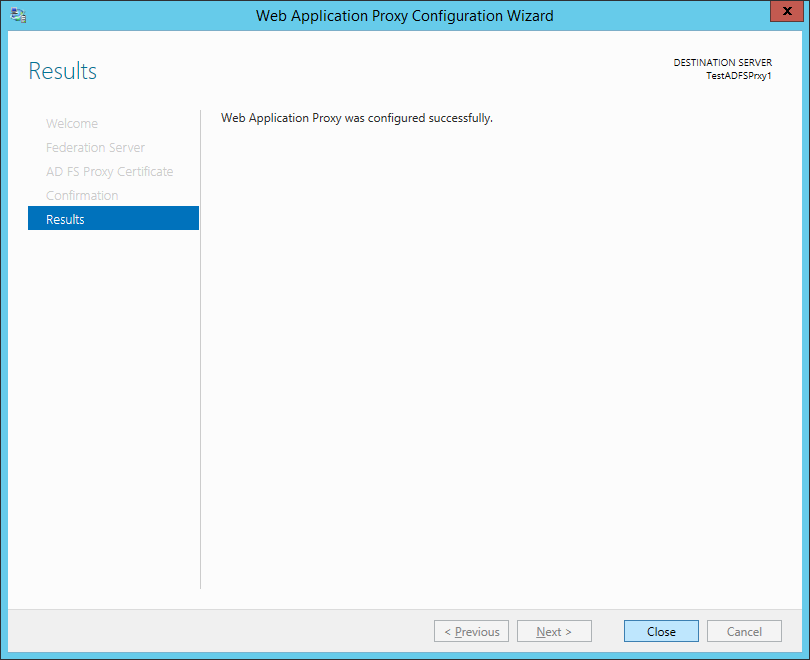
After WAP successfully connects to the ADFS service and confirms the certificate and create a proxy trust by using the given account, we see the below screen.
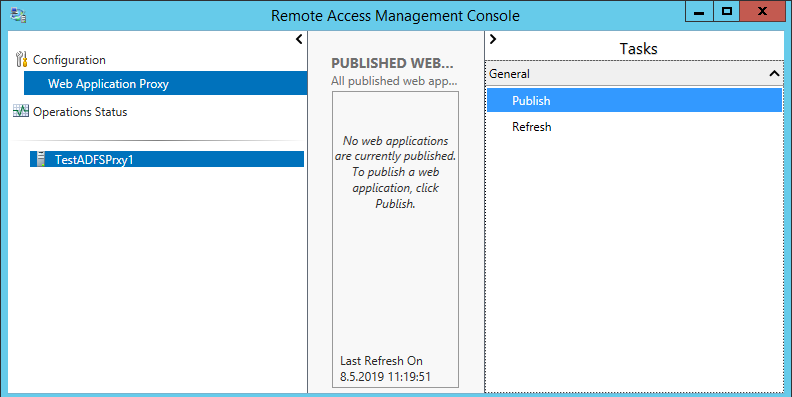
Once you click Close button, Remote Access Management Console will automatically open.
If you have any other servers to add as a WAP, repeat the above steps on the servers at this phase. After they are ready as well.
Go to the first WAP server.
Click Publish in the right menu to create a new pass-through publishing

Select Pass-through preauthentiation
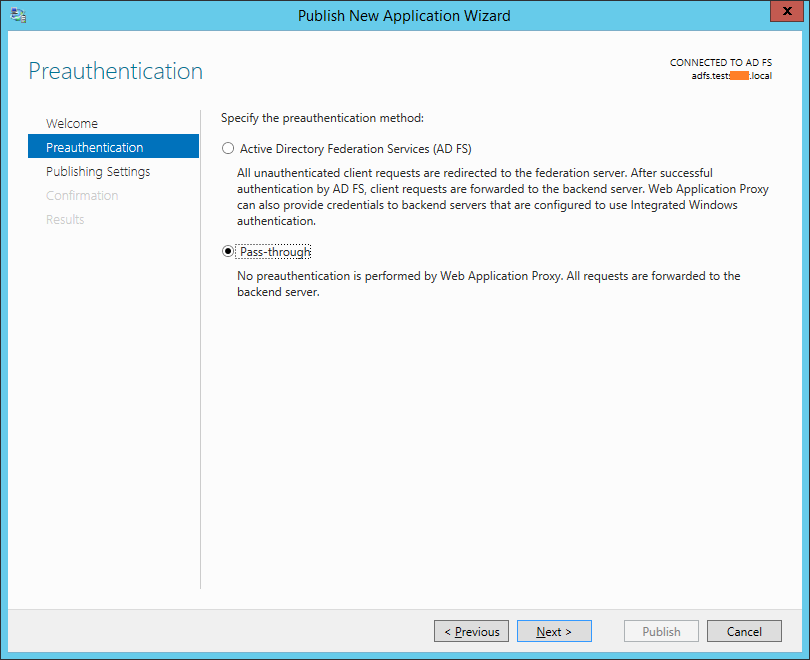
External and Backend server URL must be the same. Normally your certificate in a production environment would be yourdomain.com or yourdomain.net or someting reachable from public network.

Click Publish

We successfully published.
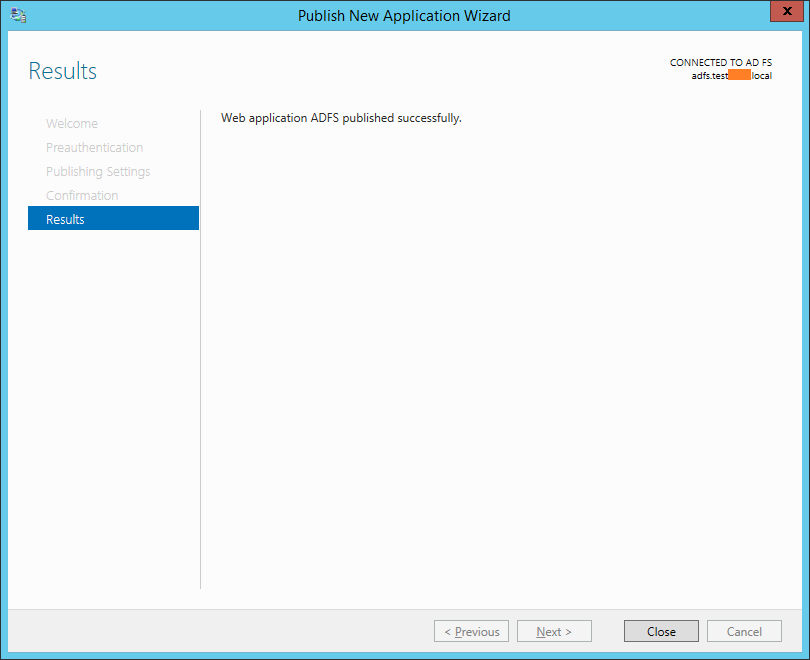
In my lab, I have setup NLB clusters between ADFS Proxy servers. Once I make a publication, remaining NLB nodes gets the configuration automatically. It will be enough to Refresh the Remote Access management Console.
From Operations Status, you can see if the servers are working properly.

The rest is about a firewall port forwarding rule and Host A record on the public DNS.
TroubleShooting: After I added the second Web Application Proxy, I saw a error message "Either the server is not working properly or credentials are not available to manage or monitor it"under the Operations Status section. I tried to re-enter the credentials but it was not working.

Solution:
Open Windows PowerShell as Administrator on all WAP Servers and run the following command:
Enable-PSRemoting –force
Lets see the list all TrustedHosts (The list will come empty)
Get-Item WSMan:\localhost\Client\TrustedHosts
We need to add WAP servers in trustedHosts List for eachother
Run this command on Proxy1
Set-Item WSMan:\localhost\Client\TrustedHosts -Value 'YOURWAPSERVER2' -Concatenate
and Run this on the Proxy2
Set-Item WSMan:\localhost\Client\TrustedHosts -Value 'YOURWAPSERVER1' -Concatenate
Lets see the list all TrustedHosts once more:
Get-Item WSMan:\localhost\Client\TrustedHosts
If you make a mistake you can clear the TrustedHosts list with this command
Set-Item WSMan:\localhost\Client\TrustedHosts -Value ''
And my issue is solved.

- Hits: 3907